The KZG Ceremony was the most important multi-party computation of its sort (by variety of individuals). Via an open, accessible course of, it produced a safe cryptographic basis for EIP-4844.
Study extra about how the Ceremony labored in Carl Beekhuizen’s Devcon discuss: “Summoning the spirit of the Dankshard”
Because the Dencun improve approaches, this put up will function a complete report of outcomes and those who introduced the Ceremony to life in 2023.
Outcomes and Strategies
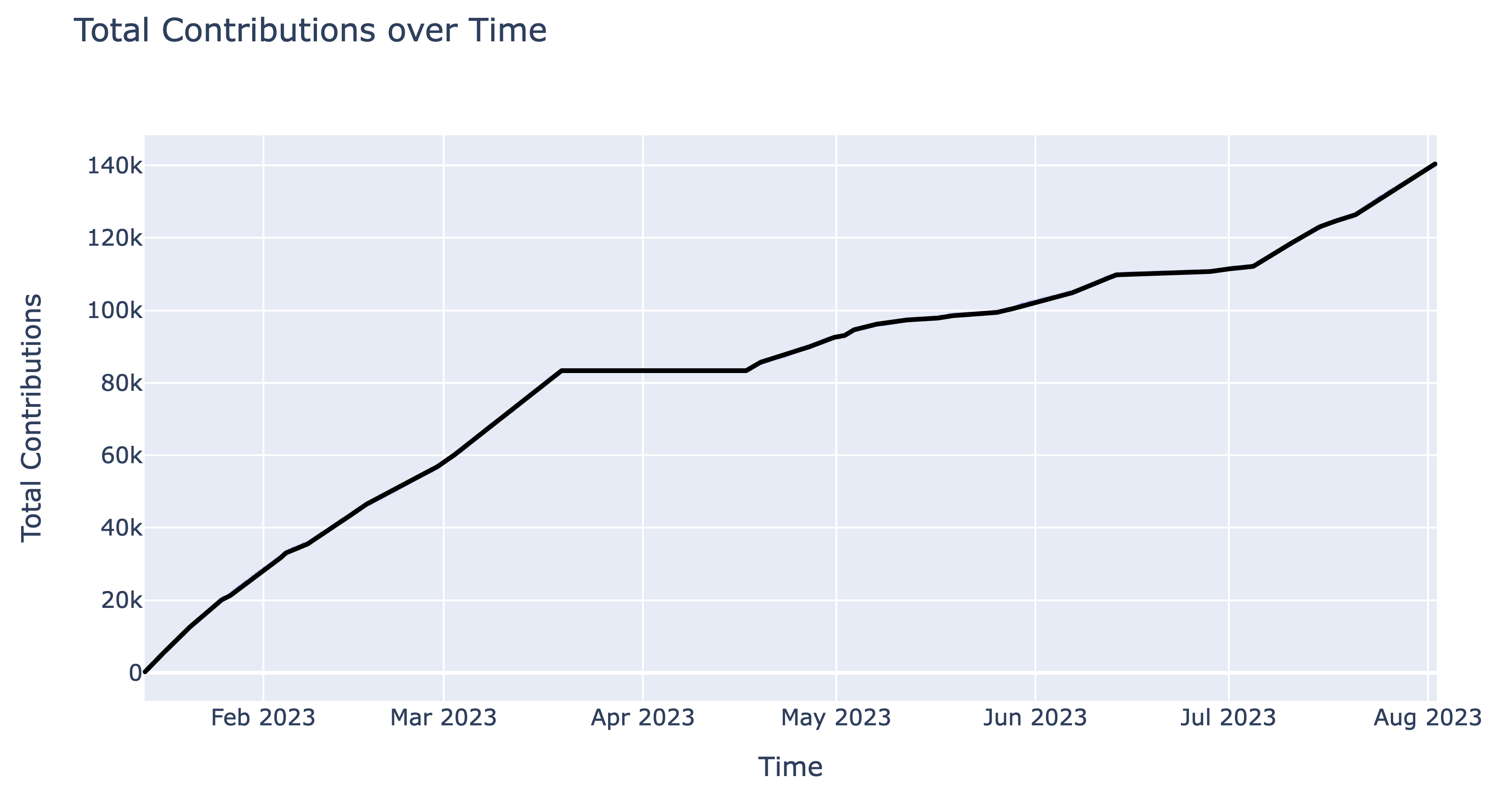
The Ceremony ran for 208 days: from Jan 13 13:13 UTC 2023 till Aug 08 23:08 UTC 2023
141,416 contributions made this the most important setup of this sort on the time of publishing.
Contributors have been required to sign-in by way of Github or authenticate utilizing an Ethereum handle for spam prevention.
- 132,021 (93.36%) used Sign up with Ethereum
- 9,395 (6.64%) used Github
As further spam prevention, Ethereum addresses have been required to have despatched a sure variety of transactions (additionally known as “nonce”) earlier than the beginning of the Ceremony at block 16,394,155 2023/01/13 00:00 UTC. This requirement was modified all through, relying on the wants at the moment.
- Jan 13 – March 13: nonce 3
- March 13 – April 01: no new logins, however the foyer was allowed to filter, ie. anybody already logged-in was in a position to full their contribution.
- April 01-16: public contributions closed to accommodate Particular Contributions
- April 16-25: 128
- April 25-Might 8: 64
- Might 8-25: 32
- Might 25 – June 27: 16
- June 27 – Aug 23: 8
To stop bots or scripts from interrupting trustworthy contributors, the method was set as much as blacklist any accounts with extreme logins/pings. To reset trustworthy accounts by accident added to the record, the blacklist was cleared 4 occasions all through the contribution interval.
Please be aware that we don’t suggest utilizing KZG contributions as a dependable record of distinctive identities e.g. for airdrops. Whereas the sign-in and nonce necessities inspired trustworthy entropy contributions, these have been in the end minor impediments to actors desirous to contribute a number of occasions. Evaluation of the transcript and onchain exercise clearly present that many contributions got here from linked addresses managed by single entities. Fortuitously, as a result of these contributions have been nonetheless including entropy, it does not detract from the soundness of the ultimate transcript output.
Verifying the transcript
8ed1c73857e77ae98ea23e36cdcf828ccbf32b423fddc7480de658f9d116c848: is the sha-256 hash of the ultimate transcript output.
The transcript is 242 MB, and is accessible on GitHub within the ethereum/kzg-ceremony repo or by way of IPFS underneath the CID QmZ5zgyg1i7ixhDjbUM2fmVpES1s9NQfYBM2twgrTSahdy.
There are a number of technique of verifying the transcript. It may be explored and verified on ceremony.ethereum.org, or with a devoted verification script written in rust.
Study extra in regards to the checks applied right here in Geoff’s weblog put up: Verifying the KZG Ceremony Transcript.
There was a commemorative POAP NFT which might be claimed by contributors who logged in with their Ethereum handle. The design of the POAP matches that of the unique hosted interface, and consists of the hash of the transcript within the border (8ed…848). So far, over 76k NFTs have been claimed by individuals. Anybody who verified the transcript output was additionally in a position to tweet as social proof of success: see current verification tweets right here.
As famous above, we don’t suggest utilizing the record of minted POAPs as a robust anti-sybil sign, eg. for airdrop eligibility.
Particular Contributions
April 1-16 2023 was the Particular Contribution Interval for the KZG Ceremony. This allowed individuals to contribute in methods that will not have been doable within the Open Contribution interval.
Whereas the Ceremony solely wants a single trustworthy participant to offer a safe output, Particular Contributions present further assurances past a typical entropy contribution:
- computing over the entropy in an remoted atmosphere (eg. on an air-gapped machine, wiping and bodily destroying {hardware}) means it is unlikely for a malicious entity to have extracted the entropy at any level
- detailed documentation (discover hyperlinks beneath) connected to actual reputations are unlikely to all have been coopted or faked by a malicious coordinating entity. The information can be found for future observers to discover.
- completely different {hardware} and software program limits correlated threat
- differentiated entropy era (eg. measuring an explosion) prevents the Ceremony output being compromised by some failure within the common entropy era (eg. the hosted interface)
- contributions involving massive teams of individuals are more durable to pretend than these with just one individual
See the unique Ethereum weblog put up which paperwork the 14 particular contributions: particulars on methodology, the place to search out them within the transcript, and hyperlinks to documenting media.
- Cryptosat: entropy from house
- The KZG Marble Machine: 3d printed marble machine
- Mr. Moloch’s Ephemeral Album II: a day-long musical journey
- Canine Dinner Dance Dynamics: a great boy get dinner
- CZG-Keremony: a pure JS KZG ceremony consumer
- Improvised Theatre: unpredictable improv
- A Calculating Automobile: Self-driving automobile collects information
- A loud metropolis: Sydney whispers its tales
- Exothermic Entropy: chemical substances go increase
- The Sferic Undertaking: lightning by no means strikes in the identical place twice
- The Nice Belgian Beer Entropy Caper: recording an evening of beer with a pal
- KZGamer: summoning Dankshard with a dice-tower
- Catropy: cats proceed being integral to the web
- srsly: an iOS KZG Ceremony consumer
The assets listed below are useful to study extra about how these constructions work, each usually and with regard to Ethereum’s specific context.
| Title | Venue | Individuals | Launch Date |
|---|---|---|---|
| Danksharding and the KZG Ceremony w/ Carl Beekhuizen (Ethereum Basis) | Unusual Water Podcast | Rex, Carl Beekhuizen | November 2023 |
| KZG Ceremony Duo Summons The Ethereum Street Map | The Defiant | Tegan Kline, Carl Beekhuizen, Trent Van Epps | April 2023 |
| Episode 262: Ethereum’s KZG Ceremony with Trent & Carl | Zero Data | Anna Rose, Kobi Gurkan, Carl Beekhuizen, Trent Van Epps | Feb 2023 |
| Ethereum’s KZG Ceremony | Bankless | David Hoffman, Trent Van Epps, Carl Beekhuizen | Jan 2023 |
| Peep an EIP – KZG Ceremony | EthCatHerders | Pooja Ranjan, Carl Beekhuizen | Jan 2023 |
| Ethereum Basis – EIP-4844 & KZG Ceremony | Epicenter | Friederike Ernst, Trent Van Epps, Carl Beekhuizen | Jan 2023 |
| Constructing the KZG Ceremony | PSE Study and Share | Nico Serrano, Geoff Lamperd | Dec 2022 |
| The KZG Ceremony – or How I Learnt to Cease Worrying and Love Trusted Setups | Devcon | Carl Beekhuizen | Oct 2022 |
Audits
Given the utmost significance of safety on this challenge, two audits have been carried out, every for various parts.
Consumer Implementations
There have been quite a lot of unbiased implementations that Ceremony individuals might run domestically, with a wide range of completely different options.
CLI Interfaces
| Implementation | BLS Library | Language | License | Writer | Notes |
|---|---|---|---|---|---|
| Chotto | blst (jblst) | Java | Apache 2.0 | Stefan Bratanov (@StefanBratanov) | |
| go-kzg-ceremony-client | gnark-crypto | Go | MIT | Ignacio Hagopian (@jsign) | Options: transcript verification, utilizing further exterior sources of entropy, eg. drand community, an arbitrary URL offered by the person. Notice: double signing not supported on account of lack of hash-to-curve in gnark. |
| eth-KZG-ceremony-alt | kilic | Go | GPL-3.0 | Arnaucube (@arnaucube) | |
| Towers of Pau | blst | Go | MIT | Daniel Knopik (@dknopik), Marius van der Wijden (@MariusVanDerWijden) | Linux solely, no signatures. |
| cpp-kzg-ceremony-client | blst | C++ | AGPL-3.0 | Patrice Vignola (@PatriceVignola) | Options: BLS/ECDSA signing, transcript verification, Linux/Home windows/MacOS assist |
| czg-keremony | noble-curves | JavaScript | MIT | JoonKyo Kim (@rootwarp), HyungGi Kim (@kim201212) | |
| kzg-ceremony-client | blst | C# | MIT | Alexey (@flcl42), CheeChyuan (@chee-chyuan), Michal (@mpzajac), Jorge (@jmederosalvarado), Prince (@prix0007) |
Browser Interfaces
- audit: QmevfvaP3nR5iMncWKa55B2f5mUgTAw9oDjFovD3XNrJTV
- doge: QmRs83zAU1hEnPHeeSKBUa58kLiWiwkjG3rJCmB8ViTcSU
BLS Libraries
A large shout out to the handfuls of individuals from the broader Ethereum neighborhood concerned in design, coordination, audits, devops-ing, and writing code. This challenge wouldn’t have existed with out your efforts!
One other thanks to the tens of hundreds of people that took the time to contribute, report bugs, and assist scale Ethereum.