Particular due to Vlad Zamfir for a lot of the pondering behind multi-chain cryptoeconomic paradigms
First off, a historical past lesson. In October 2013, once I was visiting Israel as a part of my journey across the Bitcoin world, I got here to know the core groups behind the coloured cash and Mastercoin tasks. As soon as I correctly understood Mastercoin and its potential, I used to be instantly drawn in by the sheer energy of the protocol; nonetheless, I disliked the truth that the protocol was designed as a disparate ensemble of “options”, offering a subtantial quantity of performance for folks to make use of, however providing no freedom to flee out of that field. Searching for to enhance Mastercoin’s potential, I got here up with a draft proposal for one thing referred to as “final scripting” – a general-purpose stack-based programming language that Mastercoin may embrace to permit two events to make a contract on an arbitrary mathematical method. The scheme would generalize financial savings wallets, contracts for distinction, many sorts of playing, amongst different options. It was nonetheless fairly restricted, permitting solely three phases (open, fill, resolve) and no inside reminiscence and being restricted to 2 events per contract, but it surely was the primary true seed of the Ethereum thought.
I submitted the proposal to the Mastercoin crew. They had been impressed, however elected to not undertake it too rapidly out of a want to be gradual and conservative; a philosophy which the undertaking retains to to today and which David Johnston talked about on the current Tel Aviv convention as Mastercoin’s major differentiating characteristic. Thus, I made a decision to exit alone and easily construct the factor myself. Over the following three weeks I created the unique Ethereum whitepaper (sadly now gone, however a nonetheless very early model exists right here). The fundamental constructing blocks had been all there, besides the progamming language was register-based as a substitute of stack-based, and, as a result of I used to be/am not expert sufficient in p2p networking to construct an unbiased blockchain shopper from scratch, it was to be constructed as a meta-protocol on high of Primecoin – not Bitcoin, as a result of I needed to fulfill the considerations of Bitcoin builders who had been indignant at meta-protocols bloating the blockchain with additional knowledge.
As soon as competent builders like Gavin Wooden and Jeffrey Wilcke, who didn’t share my deficiencies in capability to write down p2p networking code, joined the undertaking, and as soon as sufficient folks had been excited that I noticed there could be cash to rent extra, I made the choice to instantly transfer to an unbiased blockchain. The reasoning for this selection I described in my whitepaper in early January:
The benefit of a metacoin protocol is that it will possibly enable for extra superior transaction varieties, together with customized currencies, decentralized alternate, derivatives, and so on, which might be unattainable on high of Bitcoin itself. Nevertheless, metacoins on high of Bitcoin have one main flaw: simplified cost verification, already troublesome with coloured cash, is outright unattainable on a metacoin. The reason being that whereas one can use SPV to find out that there’s a transaction sending 30 metacoins to handle X, that by itself doesn’t imply that deal with X has 30 metacoins; what if the sender of the transaction didn’t have 30 metacoins to start out with and so the transaction is invalid? Discovering out any half of the present state basically requires scanning via all transactions going again to the metacoin’s unique launch to determine which transactions are legitimate and which of them should not. This makes it unattainable to have a really safe shopper with out downloading your complete 12 GB Bitcoin blockchain.
Basically, metacoins do not work for gentle purchasers, making them reasonably insecure for smartphones, customers with previous computer systems, internet-of-things units, and as soon as the blockchain scales sufficient for desktop customers as effectively. Ethereum’s unbiased blockchain, then again, is particularly designed with a extremely superior gentle shopper protocol; in contrast to with meta-protocols, contracts on high of Ethereum inherit the Ethereum blockchain’s gentle client-friendliness properties absolutely. Lastly, lengthy after that, I spotted that by making an unbiased blockchain permits us to experiment with stronger variations of GHOST-style protocols, safely flattening the block time to 12 seconds.
So what is the level of this story? Basically, had historical past been completely different, we simply may have gone the route of being “on high of Bitcoin” proper from day one (the truth is, we nonetheless may make that pivot if desired), however strong technical causes existed then why we deemed it higher to construct an unbiased blockchain, and these causes nonetheless exist, in just about precisely the identical kind, right this moment.
Since a lot of readers had been anticipating a response to how Ethereum as an unbiased blockchain could be helpful even within the face of the current announcement of a metacoin primarily based on Ethereum know-how, that is it. Scalability. If you happen to use a metacoin on BTC, you acquire the good thing about having simpler back-and-forth interplay with the Bitcoin blockchain, however if you happen to create an unbiased chain then you’ve the flexibility to realize a lot stronger ensures of safety significantly for weak units. There are definitely functions for which the next diploma of connectivity with BTC is essential ; for these instances a metacoin would definitely be superior (though observe that even an unbiased blockchain can work together with BTC fairly effectively utilizing mainly the identical know-how that we’ll describe in the remainder of this weblog submit). Thus, on the entire, it would definitely assist the ecosystem if the identical standardized EVM is out there throughout all platforms.
Past 1.0
Nevertheless, in the long run, even gentle purchasers are an unsightly resolution. If we actually anticipate cryptoeconomic platforms to turn into a base layer for a really great amount of worldwide infrastructure, then there might effectively find yourself being so many crypto-transactions altogether that no laptop, besides possibly just a few very massive server farms run by the likes of Google and Amazon, is highly effective sufficient to course of all of them. Thus, we have to break the elemental barrier of cryptocurrency: that there have to exist nodes that course of each transaction. Breaking that barrier is what will get a cryptoeconomic platform’s database from being merely massively replicated to being actually distributed. Nevertheless, breaking the barrier is difficult, significantly if you happen to nonetheless wish to keep the requirement that all the completely different elements of the ecosystem ought to reinforce one another’s safety.
To realize the aim, there are three main methods:
- Constructing protocols on high of Ethereum that use Ethereum solely as an auditing-backend-of-last-resort, conserving transaction charges.
- Turning the blockchain into one thing a lot nearer to a high-dimensional interlinking mesh with all elements of the database reinforcing one another over time.
- Going again to a mannequin of one-protocol (or one service)-per-chain, and arising with mechanisms for the chains to (1) work together, and (2) share consensus energy.
Of those methods, observe that solely (1) is in the end suitable with conserving the blockchain in a kind something near what the Bitcoin and Ethereum protocols help right this moment. (2) requires a large redesign of the elemental infrastructure, and (3) requires the creation of 1000’s of chains, and for fragility mitigation functions the optimum strategy shall be to make use of 1000’s of currencies (to scale back the complexity on the consumer facet, we will use stable-coins to basically create a standard cross-chain forex commonplace, and any slight swings within the stable-coins on the consumer facet could be interpreted within the UI as curiosity or demurrage so the consumer solely must maintain monitor of 1 unit of account).
We already mentioned (1) and (2) in earlier weblog posts, and so right this moment we are going to present an introduction to among the rules concerned in (3).
Multichain
The mannequin right here is in some ways much like the Bitshares mannequin, besides that we don’t assume that DPOS (or another POS) shall be safe for arbitrarily small chains. Somewhat, seeing the final sturdy parallels between cryptoeconomics and establishments in wider society, significantly authorized techniques, we observe that there exists a big physique of shareholder regulation defending minority stakeholders in real-world corporations towards the equal of a 51% assault (specifically, 51% of shareholders voting to pay 100% of funds to themselves), and so we attempt to replicate the identical system right here by having each chain, to some extent, “police” each different chain both straight or not directly via an interlinking transitive graph. The type of policing required is straightforward – policing aganist double-spends and censorship assaults from native majority coalitions, and so the related guard mechanisms might be carried out solely in code.
Nevertheless, earlier than we get to the arduous drawback of inter-chain safety, allow us to first talk about what really seems to be a a lot simpler drawback: inter-chain interplay. What will we imply by a number of chains “interacting”? Formally, the phrase can imply considered one of two issues:
- Inside entities (ie. scripts, contracts) in chain A are in a position to securely be taught details in regards to the state of chain B (info switch)
- It’s potential to create a pair of transactions, T in A and T’ in B, such that both each T and T’ get confirmed or neither do (atomic transactions)
A sufficiently normal implementation of (1) implies (2), since “T’ was (or was not) confirmed in B” is a reality in regards to the state of chain B. The best means to do that is by way of Merkle bushes, described in additional element right here and right here; basically Merkle bushes enable your complete state of a blockchain to be hashed into the block header in such a means that one can give you a “proof” {that a} specific worth is at a specific place within the tree that’s solely logarithmic in measurement in your complete state (ie. at most just a few kilobytes lengthy). The final thought is that contracts in a single chain validate these Merkle tree proofs of contracts within the different chain.
A problem that’s higher for some consensus algorithms than others is, how does the contract in a sequence validate the precise blocks in one other chain? Basically, what you find yourself having is a contract appearing as a fully-fledged “gentle shopper” for the opposite chain, processing blocks in that chain and probabilistically verifying transactions (and conserving monitor of challenges) to make sure safety. For this mechanism to be viable, at the very least some amount of proof of labor should exist on every block, in order that it’s not potential to cheaply produce many blocks for which it’s arduous to find out that they’re invalid; as a normal rule, the work required by the blockmaker to provide a block ought to exceed the price to your complete community mixed of rejecting it.
Moreover, we must always observe that contracts are silly; they don’t seem to be able to status, social consensus or another such “fuzzy” metrics of whether or not or not a given blockchain is legitimate; therefore, purely “subjective” Ripple-style consensus shall be troublesome to make work in a multi-chain setting. Bitcoin’s proof of labor is (absolutely in principle, largely in apply) “goal”: there’s a exact definition of what the present state is (specifically, the state reached by processing the chain with the longest proof of labor), and any node on the planet, seeing the gathering of all accessible blocks, will come to the identical conclusion on which chain (and subsequently which state) is appropriate. Proof-of-stake techniques, opposite to what many cryptocurrency builders suppose, might be safe, however have to be “weakly subjective” – that’s, nodes that had been on-line at the very least as soon as each N days for the reason that chain’s inception will essentially converge on the identical conclusion, however long-dormant nodes and new nodes want a hash as an preliminary pointer. That is wanted to forestall sure lessons of unavoidable long-range assaults. Weakly subjective consensus works high quality with contracts-as-automated-light-clients, since contracts are all the time “on-line”.
Word that it’s potential to help atomic transactions with out info switch; TierNolan’s secret revelation protocol can be utilized to do that even between comparatively dumb chains like BTC and DOGE. Therefore, generally interplay shouldn’t be too troublesome.
Safety
The bigger drawback, nonetheless, is safety. Blockchains are susceptible to 51% assaults, and smaller blockchains are susceptible to smaller 51% assaults. Ideally, if we wish safety, we wish for a number of chains to have the ability to piggyback on one another’s safety, in order that no chain might be attacked except each chain is attacked on the identical time. Inside this framework, there are two main paradigm selections that we will make: centralized or decentralized.
| Centralized | Decentralized |
 |
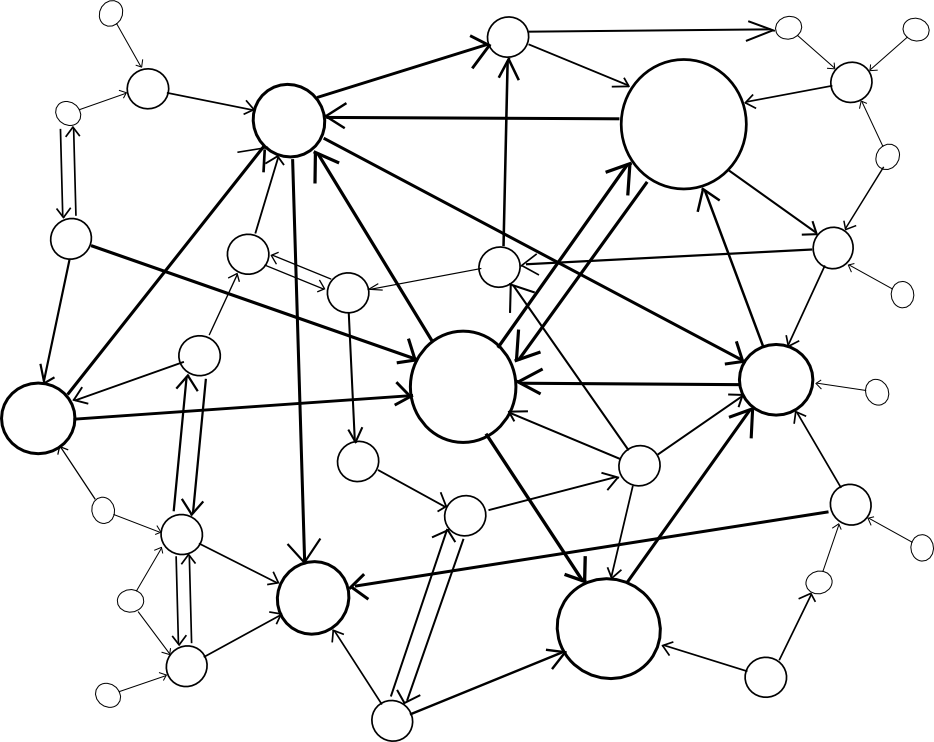 |
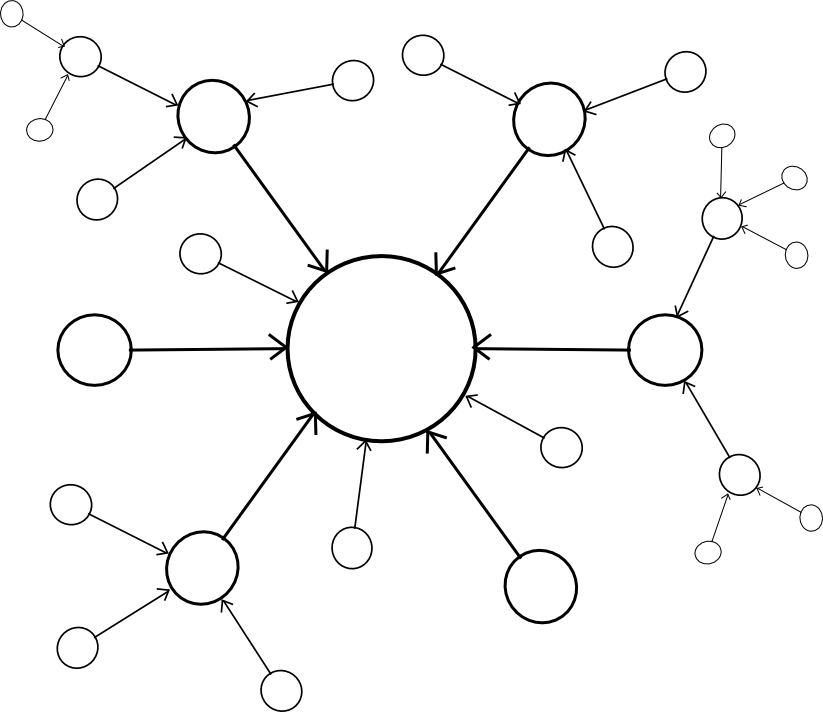
A centralized paradigm is actually each chain, whether or not straight or not directly, piggybacking off of a single grasp chain; Bitcoin proponents typically like to see the central chain being Bitcoin, although sadly it could be one thing else since Bitcoin was not precisely designed with the required stage of general-purpose performance in thoughts. A decentralized paradigm is one that appears vaguely like Ripple’s community of distinctive node lists, besides working throughout chains: each chain has a listing of different consensus mechanisms that it trusts, and people mechanisms collectively decide block validity.
The centralized paradigm has the profit that it is easier; the decentralized paradigm has the profit that it permits for a cryptoeconomy to extra simply swap out completely different items for one another, so it doesn’t find yourself resting on many years of outdated protocols. Nevertheless, the query is, how will we really “piggyback” on a number of different chains’ safety?
To offer a solution to this query, we’ll first give you a formalism referred to as an assisted scoring perform. Usually, the way in which blockchains work is that they have some scoring perform for blocks, and the top-scoring block turns into the block defining the present state. Assisted scoring features work by scoring blocks primarily based on not simply the blocks themselves, but additionally checkpoints in another chain (or a number of chains). The final precept is that we use the checkpoints to find out {that a} given fork, regardless that it could seem like dominant from the viewpoint of the native chain, might be decided to have come later via the checkpointing course of.
A easy strategy is {that a} node penalizes forks the place the blocks are too far other than one another in time, the place the time of a block is set by the median of the earliest identified checkpoint of that block within the different chains; this is able to detect and penalize forks that occur after the very fact. Nevertheless, there are two issues with this strategy:
- An attacker can submit the hashes of the blocks into the checkpoint chains on time, after which solely reveal the blocks later
- An attacker might merely let two forks of a blockchain develop roughly evenly concurrently, after which finally push on his most well-liked fork with full power
To cope with (2), we will say that solely the legitimate block of a given block quantity with the earliest common checkpointing time might be a part of the principle chain, thus basically fully stopping double-spends and even censorship forks; each new block would have to level to the final identified earlier block. Nevertheless, this does nothing towards (1). To resolve (1), one of the best normal options contain some idea of “voting on knowledge availability” (see additionally: Jasper den Ouden’s earlier submit speaking a few comparable thought); basically, the contributors within the checkpointing contract on every of the opposite chains would Schelling-vote on whether or not or not your complete knowledge of the block was accessible on the time the checkpoint was made, and a checkpoint could be rejected if the vote leans towards “no”.
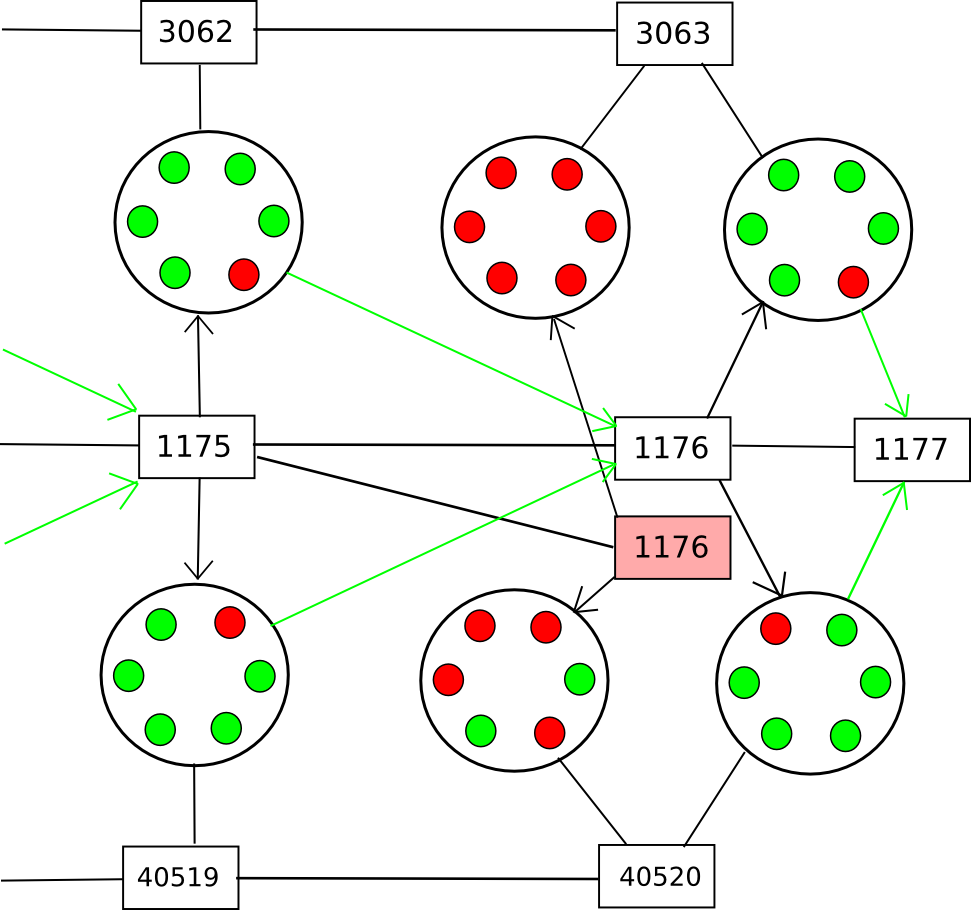
Word that there are two variations of this technique. The primary is a method the place contributors vote on knowledge availability solely (ie. that each a part of the block is on the market on-line). This permits the voters to be reasonably silly, and be capable to vote on availability for any blockchain; the method for figuring out knowledge availability merely consists of repeatedly doing a reverse hash lookup question on the community till all of the “leaf nodes” are discovered and ensuring that nothing is lacking. A intelligent option to power nodes to not be lazy when doing this test is to ask them to recompute and vote on the foundation hash of the block utilizing a special hash perform. As soon as all the info is out there, if the block is invalid an environment friendly Merkle-tree proof of invalidity might be submitted to the contract (or just revealed and left for nodes to obtain when figuring out whether or not or to not rely the given checkpoint).
The second technique is much less modular: have the Schelling-vote contributors vote on block validity. This may make the method considerably easier, however at the price of making it extra chain-specific: you would want to have the supply code for a given blockchain so as to have the ability to vote on it. Thus, you’d get fewer voters offering safety to your chain mechanically. No matter which of those two methods is used, the chain may subsidize the Schelling-vote contract on the opposite chain(s) by way of a cross-chain alternate.
The Scalability Half
Up till now, we nonetheless have no precise “scalability”; a sequence is simply as safe because the variety of nodes which might be keen to obtain (though not course of) each block. After all, there are answers to this drawback: challenge-response protocols and randomly chosen juries, each described in the earlier weblog submit on hypercubes, are the 2 which might be at present best-known. Nevertheless, the answer right here is considerably completely different: as a substitute of setting in stone and institutionalizing one specific algorithm, we’re merely going to let the market resolve.
The “market” is outlined as follows:
- Chains wish to be safe, and wish to save on assets. Chains want to pick out a number of Schelling-vote contracts (or different mechanisms probably) to function sources of safety (demand)
- Schelling-vote contracts function sources of safety (provide). Schelling-vote contracts differ on how a lot they have to be backed with a view to safe a given stage of participation (worth) and the way troublesome it’s for an attacker to bribe or take over the schelling-vote to power it to ship an incorrect consequence (high quality).
Therefore, the cryptoeconomy will naturally gravitate towards schelling-vote contracts that present higher safety at a lower cost, and the customers of these contracts will profit from being afforded extra voting alternatives. Nevertheless, merely saying that an incentive exists shouldn’t be sufficient; a reasonably massive incentive exists to remedy ageing and we’re nonetheless fairly removed from that. We additionally want to point out that scalability is definitely potential.
The higher of the 2 algorithms described within the submit on hypercubes, jury choice, is straightforward. For each block, a random 200 nodes are chosen to vote on it. The set of 200 is sort of as safe as your complete set of voters, for the reason that particular 200 should not picked forward of time and an attacker would want to manage over 40% of the contributors with a view to have any important likelihood of getting 50% of any set of 200. If we’re separating voting on knowledge availability from voting on validity, then these 200 might be chosen from the set of all contributors in a single summary Schelling-voting contract on the chain, because it’s potential to vote on the info availability of a block with out really understanding something in regards to the blockchain’s guidelines. Thus, as a substitute of each node within the community validating the block, solely 200 validate the info, after which just a few nodes have to search for precise errors, since if even one node finds an error it is going to be in a position to assemble a proof and warn everybody else.
Conclusion
So, what’s the finish results of all this? Basically, now we have 1000’s of chains, some with one software, but additionally with general-purpose chains like Ethereum as a result of some functions profit from the extraordinarily tight interoperability that being inside a single digital machine provides. Every chain would outsource the important thing a part of consensus to a number of voting mechanisms on different chains, and these mechanisms could be organized in several methods to ensure they’re as incorruptible as potential. As a result of safety might be taken from all chains, a big portion of the stake in your complete cryptoeconomy could be used to guard each chain.
It could show essential to sacrifice safety to some extent; if an attacker has 26% of the stake then the attacker can do a 51% takeover of 51% of the subcontracted voting mechanisms or Schelling-pools on the market; nonetheless, 26% of stake remains to be a big safety margin to have in a hypothetical multi-trillion-dollar cryptoeconomy, and so the tradeoff could also be price it.
The true good thing about this sort of scheme is simply how little must be standardized. Every chain, upon creation, can select some variety of Schelling-voting swimming pools to belief and subsidize for safety, and by way of a custom-made contract it will possibly modify to any interface. Merkle bushes will have to be suitable with all the completely different voting swimming pools, however the one factor that must be standardized there may be the hash algorithm. Completely different chains can use completely different currencies, utilizing stable-coins to supply a fairly constant cross-chain unit of worth (and, in fact, these stable-coins can themselves work together with different chains that implement varied sorts of endogenous and exogenous estimators). In the end, the imaginative and prescient of considered one of 1000’s of chains, with the completely different chains “shopping for providers” from one another. Providers would possibly embrace knowledge availability checking, timestamping, normal info provision (eg. worth feeds, estimators), non-public knowledge storage (probably even consensus on non-public knowledge by way of secret sharing), and way more. The final word distributed crypto-economy.

